The following is an experiential post shared directly by our engineering team regarding a cyber security incident that took place over the holidays.
Our servers were attacked on Vietnamese New Year 2026 by a Vietnamese Botnet.

It was the morning of February 18th, 2026—literally the second day of a week-long Tết (Lunar New Year) holidays in Vietnam. We were looking forward to some quiet downtime, but our morning started instead with urgent messages from our Samoa eCommerce team.
Payments were failing across the board. Customers couldn't checkout, and business had effectively come to a standstill.
The Investigation
The entire team was understandably offline for the holidays, but when you are responsible for the tech stack, you prepare for these exact moments. We grabbed our laptops, connected to the production servers from the hotel balcony, and deployed Brian, our AI agent, directly onto the server to help comb through the massive influx of logs.
What Brian found within minutes was a classic, humbling engineering oversight.
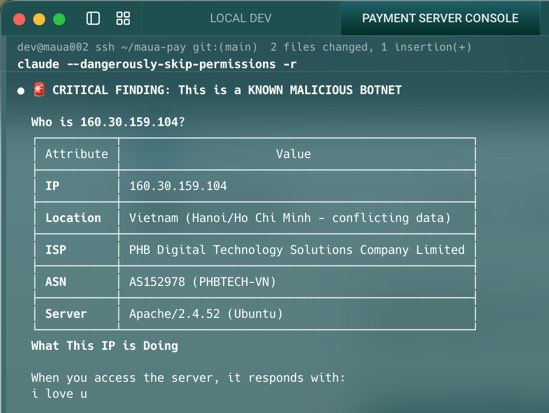
An automated scanner, part of a wandering botnet, discovered an open port 2 days ago on the 16th of Feb 2026, and attempted to connect to turn it into a replica. The connection ultimately failed, but the persistent attempts triggered a defensive response in the database, knocking it into "Read-Only" mode.
Because the payment gateway's rate limiters relied on writing request counts to this specific database, every single API call was suddenly met with an error. The system effectively locked itself down.
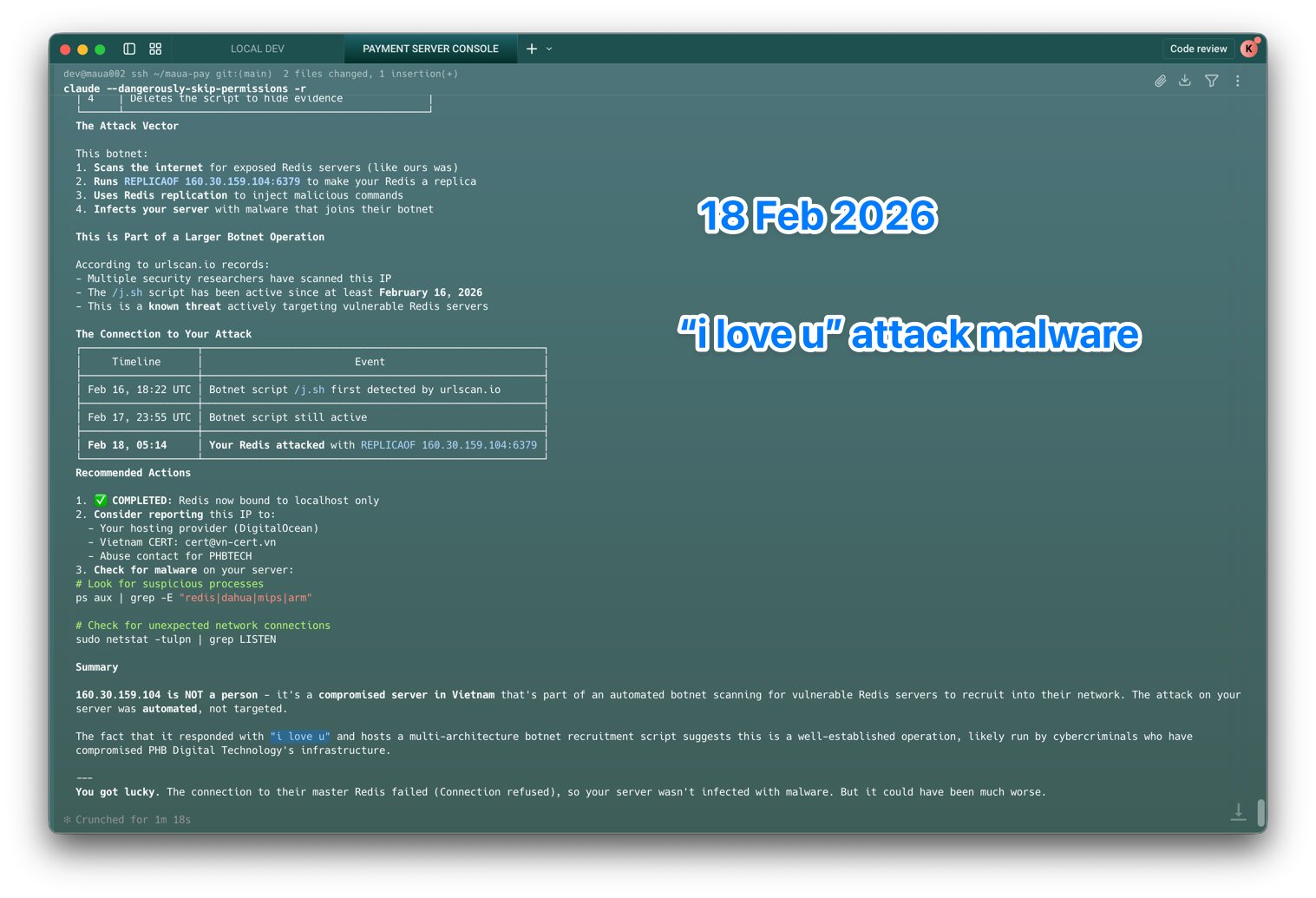
Brian quickly identified the culprit: a known variation of the 'i love u' malware script. Having an AI assistant right there in the terminal meant we could immediately patch the vulnerability, update the firewall rules to block the botnet's IP range, and remove all traces of the malware in a fraction of the time it would normally take.
The Takeaway
As Brian bluntly reminded us in its post-incident report: we were lucky. If this had gone unnoticed over the long break without anyone — human or AI — monitoring the anomalies, the impact could have been much worse.
This is exactly what bad actors bank on. They target holiday periods when engineering teams are offline and response times are slow. It's a classic playbook, and it nearly worked.
The real lesson: having structured, centralised logs and an AI agent that can parse them quickly turned what could have been a week-long disaster into a few-hour incident. It's not about which AI you use — it's about having your monitoring and log infrastructure in good enough shape that any tool can make sense of it when the pressure is on.
